Home lab: self-hosted lab as a testing ground

Actualizado: 2026-05-03
For years a home lab was an eccentricity tied to very specific enthusiasts. Today, with an old laptop, a second-hand mini PC, or a ten-euros-a-month VPS, anyone can set up a self-hosted services lab able to teach more about infrastructure than any course. This post is the one I’d have liked to find when I started: not an encyclopedic list of services, but a reflection on what a home lab delivers and how to steer it so the time invested pays off.
Key takeaways
- A useful home lab isn’t the one with the most containers, but the one that forces you to face real admin problems every week.
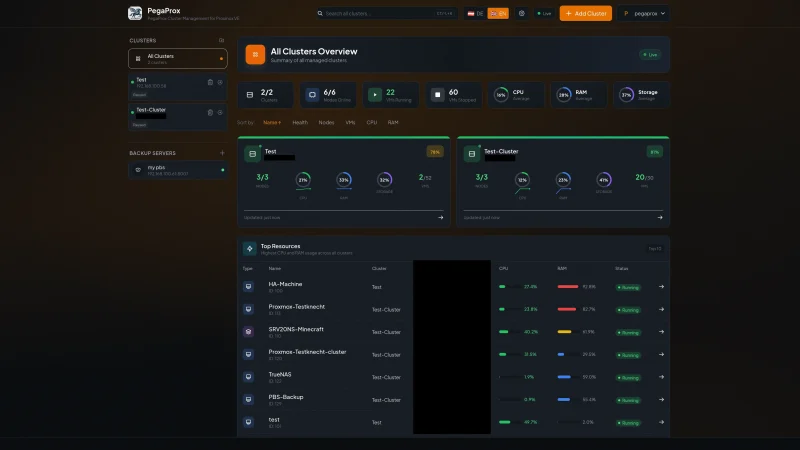
- Recommended minimal stack: reverse proxy + centralized auth + basic monitoring + serious backup tool.
- A second-hand mini PC with 16 GB of RAM is more than enough for thirty or forty containers.
- The most valuable things you learn aren’t Docker but how to think about failures, read logs, and automate with judgment.
- The real value of the home lab transfers directly to professional work.
What a useful home lab is
The temptation at first is to accumulate services: install everything that sounds interesting, run 40 containers, and end up with a tangle hard to operate. That isn’t a useful home lab.
A useful home lab is one that teaches you something every week and forces you to face real admin problems. The way to get there is to pick services you actually care about and operate them as if they were production: with backups, monitoring, alerts, automatic updates, real certificates, your own DNS, protected access. That set of practices is what you learn; the services are just the excuse to apply them.
Which services make sense
My recommendation is to start with a short stack that forces you to learn all the important layers:
- A reverse proxy as the first piece. Traefik or Caddy, both excellent. It forces you to understand DNS, TLS certificates via Let’s Encrypt, HTTP headers, domain-based routing. This component alone teaches you more than a week of tutorials.
- A centralized authentication service. Authentik or Keycloak. This dives you into OAuth 2.0 and OIDC, and lets you protect any panel or dashboard with real corporate-style login.
- A basic monitoring stack: Prometheus, Grafana, Loki for logs, Alertmanager. Configuring the first useful alerts (full disk, container down, certificate expiring) is where you move from “I have services” to “I operate services.”
- A simple secret manager. Infisical, Vault, or even a small HashiCorp Boundary. When your compose files stop having passwords in plaintext, you learn a real professional lesson.
- Backups with a serious tool. Restic is my favorite, but Borgbackup is also excellent. Setting up a remote repository (Backblaze B2, Wasabi, or rsync.net) and testing restoration before needing it is an exercise many people never do in production.
From there, add what motivates you: Nextcloud, Jellyfin, Gitea, Vaultwarden. Each service adds complexity, but also learning opportunities.
Hardware: don’t overthink it at first
The hardware you need is less than you think:
- A second-hand mini PC with 16 GB of RAM and 500 GB of SSD is more than enough for thirty or forty containers.
- A Raspberry Pi 5 also covers a basic stack, though some heavier services will require compromises.
- A mid-range VPS (Hetzner, OVH, Vultr) with 16 GB for under 25 euros a month if you don’t want anything at home.
Where it’s worth investing more is storage. If you’ll do backups seriously, a NAS or at least a dedicated external disk is more sensible than using the server’s own disk.
What you really learn
People assume a home lab teaches you Docker or Kubernetes. That’s the surface part. What you really learn, if you operate it well, is something deeper and more transferable:
- You learn to think about failures. When your own password manager stops working during an update and you can’t access anything, you discover why upstream recommends backups before each upgrade.
- You learn to read logs. When Traefik refuses to route to a service, you develop the reflex of going to logs first and the manual second. That skill is gold professionally.
- You learn to automate with judgment. After restarting a container manually three times, you write a healthcheck. After forgetting to update five times, you add automatic updates. You learn when to automate and when not to.
- You learn to operate under uncertainty. When something fails and you have no support to escalate to, you have to solve it yourself. That autonomy is the most valuable thing a home lab produces.
How to start without getting stuck
Spend two weekends setting up a minimal stack: your own domain, a small VPS, Traefik with HTTPS, an Authentik, a Grafana with Prometheus, and maybe one useful service like Vaultwarden. Leave that running for a month before adding anything.
From that solid core, add services one at a time, never two at once, and only if you’re willing to operate it. The home lab’s value isn’t in the number of containers, but in how deeply you understand each one.
After two years maintaining mine, I feel I’ve learned more than I would have in any course. And I suspect anyone who invests time with this mindset will reach the same conclusion.