Docker Scout: Vulnerabilities from Build to Registry
Actualizado: 2026-05-03
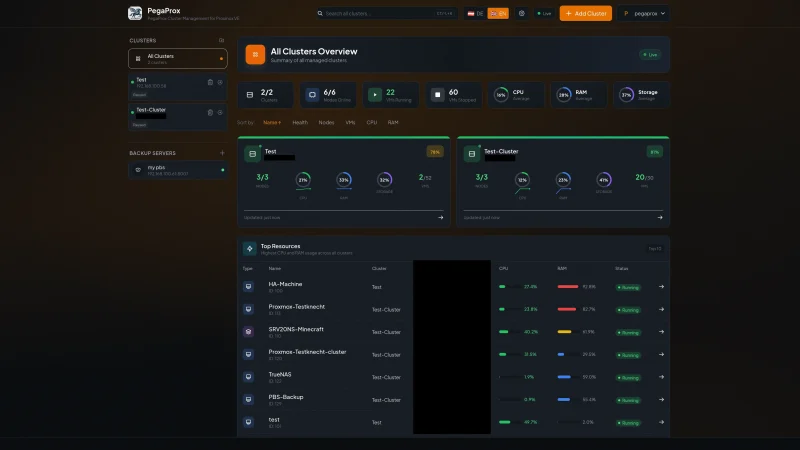
Docker Scout[1] is Docker Inc.’s attempt to enter the container-security conversation, a market that had been dominated by third-party tools for years. It reached general availability in 2023 and has matured over the past year into a visible piece inside Docker Desktop, the CLI and Docker Hub. The pitch is clean: if you already pay for Docker Hub or distribute images through it, vulnerability analysis should sit one step behind docker push, not in a separate product from a separate vendor.
Key takeaways
- Scout generates an SBOM of the image, cross-references it with NVD and ecosystem-specific feeds (GitHub Security Advisories for npm and PyPI), and reports by severity.
- Base-image recommendations are the real technical differentiator: Scout directly proposes “switch to
node:20-alpineand remove 3 critical CVEs”. - Policies turn the scanner into a real quality gate — more useful than counting CVEs.
- It is closed source and Docker-centric: if your registry is not Hub, it loses half its value.
- Trivy remains the right choice for teams with an open-source culture or auditability requirements.
What it does and how you drive it
The mental model is the usual one for any modern scanner: generate an SBOM of the image, cross-reference it against a CVE database (Scout combines Docker Hub advisories with NVD and several ecosystem-specific feeds), and report by severity. On top of that Scout adds two layers: concrete base-image adoption recommendations to eliminate CVEs, and evaluation of organisational policies that can fail a CI build.
# CVE analysis of a local image
docker scout cves my-app:1.0
# Base-image recommendations — the differentiating feature
docker scout recommendations my-app:1.0
# Diff between two tags: useful before promoting to production
docker scout compare my-app:1.1 --to my-app:1.0
# Policy evaluation against the organisation's declared rules
docker scout policy my-app:1.0In Docker Desktop the flow is even more invisible: the Images panel shows CVE counts by severity next to the tag, and a click opens the detail view with the base-image suggestion. For the developer without a security background, that zero-friction path is the product’s real strength.
CI integration and the policy model
GitHub Actions integration leans on docker/scout-action@v1, which accepts chained commands and severity filters. In a typical pipeline it pays to split two moments:
- A
comparecheck against the current production image, which catches regressions introduced by the commit. - A
cvescheck withonly-severities: critical,highandexit-code: trueas a hard quality gate.
The first prevents you from getting worse; the second enforces an absolute floor.
Policies are how Scout becomes more than a scanner: they are declarative rules evaluated against the image and its metadata. Used well, they shift the conversation from “how many CVEs does this image have” to “does this image meet the contract we’ve set for ourselves” — a far more useful question when blocking a deploy. It pairs well in a DevSecOps pipeline with Sigstore and Cosign, where image signing and CVE analysis complement each other.
Scout against Trivy, Grype and Snyk
The honest comparison is not “which finds more CVEs” — day to day they find essentially the same ones because they drink from overlapping feeds — but “which fits your operational topology”:
- Trivy wins when the team values open source (Apache 2.0), full self-hosting with no SaaS dependency, and scope beyond the container: Trivy also scans filesystems, git repositories, Kubernetes configs, and IaC.
- Grype wins when the use case centres on high-fidelity SBOM generation via Syft — the standard pipeline in organisations aligned with SLSA.
- Scout wins when the team lives inside the Docker ecosystem: Desktop as the dev tool, Hub as the registry. Base-image recommendations are its strongest technical argument.
- Snyk Container covers the entire SDLC under one umbrella — if an organisation has standardised on Snyk for code and dependencies, Scout doesn’t add enough.
Pricing: the elephant in the room
Local scanning via Docker Desktop and CLI is free. Continuous monitoring, organisation-level policies and analysis over Docker Hub repositories require Docker Team (~$11/user/month) or Docker Business (~$24). That is reasonable for a team already paying for Hub; it is expensive if all you wanted was to replace a trivy image call in CI.
Honest limitations
- Closed source: for teams with auditability requirements on the scanner itself (public sector, banking), this is blocking. Trivy or Aqua Enterprise are the alternatives.
- Docker-centrism: continuous monitoring and registry-level policies only apply on Hub. For teams migrating to GHCR, ECR or Harbor, Scout loses half its value — effectively soft vendor lock-in.
- False positives: Scout, like any scanner, reports CVEs that are inexploitable in the concrete context. The ecosystem is moving toward VEX and reachability analysis, but separating signal from noise is still manual work.
Conclusion
Docker Scout is a competent product that makes sense when the operational ecosystem is already Docker end to end. Its integration with Desktop and Hub is frictionless, its base-image recommendations are genuinely useful for developers without security expertise, and its policies allow the scan to become a real quality gate. It is not the best tool by detection capability nor the cheapest, but it is the one with the lowest friction if you already pay for Hub. For mid-sized teams without dedicated security champions, that low friction is what decides whether the tool gets used or shelved. For teams with an established open-source culture or auditability requirements, Trivy remains the correct choice.