Docker Scout: vulnerabilidades desde el build hasta el registro
Actualizado: 2026-05-03
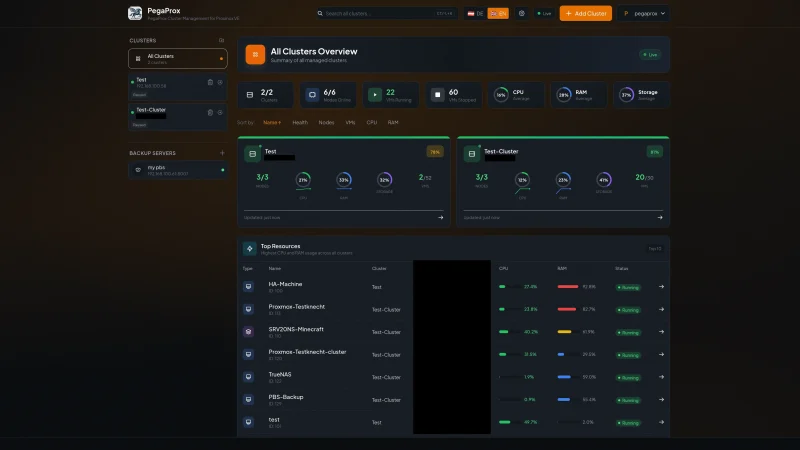
Docker Scout[1] es la apuesta de Docker Inc. por meterse en la conversación del container security, un mercado dominado por herramientas de terceros. Alcanzó disponibilidad general en 2023 y durante el último año ha madurado hasta convertirse en una pieza visible dentro de Docker Desktop, la CLI y Docker Hub. El planteamiento es claro: si ya pagas Docker Hub o distribuyes imágenes a través de él, el análisis de vulnerabilidades debería estar un paso detrás del docker push, no en otro producto de otro vendor.
Puntos clave
- Scout genera un SBOM de la imagen, lo cruza con NVD y fuentes ecosistema-específicas (GitHub Security Advisories para npm y PyPI), y reporta por severidad.
- Las recomendaciones de imagen base son el diferenciador técnico real: Scout propone directamente “cambia a
node:20-alpiney elimina 3 críticas”. - Las policies permiten convertir el escáner en un quality gate real — más útil que contar CVEs.
- Es closed source y Docker-céntrico: si tu registro no es Hub, pierde la mitad de su valor.
- Trivy sigue siendo la elección correcta para equipos con cultura open source o requisitos de auditabilidad.
Qué hace y cómo se usa
El modelo mental es el habitual de cualquier escáner moderno: se genera un SBOM de la imagen, se cruza con una base de CVE (Scout combina las advisories de Docker Hub con NVD y varias fuentes ecosistema-específicas), y se reporta por severidad. A partir de ahí Scout añade dos capas: recomendaciones concretas de qué imagen base adoptar para eliminar CVEs, y evaluación de políticas organizacionales que puede fallar el build en CI.
# Análisis CVE de una imagen local
docker scout cves my-app:1.0
# Recomendaciones de imagen base — la feature diferenciadora
docker scout recommendations my-app:1.0
# Diferencia entre dos tags: útil antes de promover a producción
docker scout compare my-app:1.1 --to my-app:1.0
# Evaluación de policies declaradas en la organización
docker scout policy my-app:1.0En Docker Desktop el flujo es aún más invisible: el panel de Images muestra el conteo de CVEs por severidad junto al tag, y un click abre el detalle con la sugerencia de imagen base. Para el desarrollador sin background en seguridad, esa fricción cero es el punto fuerte real del producto.
Integración en CI y modelo de policies
La integración con GitHub Actions se apoya en docker/scout-action@v1, que acepta comandos encadenados y filtros por severidad. En un pipeline típico conviene separar dos momentos:
- Un chequeo de
comparecontra la imagen actual de producción, que detecta regresiones introducidas por el commit. - Un chequeo de
cvescononly-severities: critical,highyexit-code: truecomo quality gate duro.
El primero previene empeorar; el segundo impone un suelo absoluto.
Las policies son el mecanismo por el que Scout se convierte en algo más que un escáner: son reglas declarativas evaluadas contra la imagen y sus metadatos. Bien usadas, desplazan la conversación de “cuántas CVEs tiene esta imagen” a “¿cumple esta imagen el contrato que nos hemos impuesto?”, que es una pregunta mucho más útil para bloquear un deploy. Encaja bien en un pipeline de DevSecOps con Sigstore y Cosign, donde la firma de la imagen y el análisis de CVEs se complementan.
Scout frente a Trivy, Grype y Snyk
La comparativa honesta no es “cuál encuentra más CVEs” — en el día a día encuentran esencialmente las mismas, porque beben de fuentes solapadas — sino “cuál encaja en tu topología operativa”:
- Trivy gana cuando el equipo valora software open source (Apache 2.0), autohospedaje completo sin dependencia de SaaS, y scope ampliado: Trivy escanea también sistemas de ficheros, repositorios git, configuraciones de Kubernetes e IaC.
- Grype gana cuando el caso de uso está centrado en SBOM de alta fidelidad vía Syft — pipeline estándar en organizaciones alineadas con SLSA.
- Scout gana cuando el equipo ya vive dentro del ecosistema Docker: Desktop como herramienta de desarrollo, Hub como registro. Las recomendaciones de imagen base son su mejor argumento técnico.
- Snyk Container cubre todo el SDLC bajo un mismo paraguas — si una organización ya ha estandarizado en Snyk para código y dependencias, Scout no aporta suficiente.
Precios: el elefante en la sala
El escaneo local con Docker Desktop y CLI es gratuito. El monitoring continuo, las policies a nivel de organización y el análisis sobre repositorios en Docker Hub requieren Docker Team (~11 USD/usuario/mes) o Docker Business (~24 USD). Es razonable para un equipo que ya paga Hub; es caro si lo único que se quería era reemplazar un trivy image en CI.
Limitaciones honestas
- Closed source: para equipos con requisitos de auditabilidad del propio escáner (sector público, banca), esto es bloqueante. Trivy o Aqua Enterprise son las alternativas.
- Docker-centrismo: el monitoring continuo y las policies a nivel de registro solo aplican en Hub. Para equipos que migran a GHCR, ECR o Harbor, Scout pierde la mitad de su valor — equivalente a un vendor lock-in encubierto.
- False positives: Scout, como cualquier escáner, reporta CVEs que son inexplotables en el contexto concreto. El ecosistema se mueve hacia VEX y reachability analysis, pero clasificar señal del ruido sigue siendo trabajo manual.
Conclusión
Docker Scout es un producto competente que tiene sentido cuando el ecosistema operativo ya es Docker de extremo a extremo. Su integración con Desktop y Hub es frictionless, sus recomendaciones de imagen base son genuinamente útiles para developers sin expertise en seguridad, y sus policies permiten convertir el escaneo en quality gate real. No es la mejor herramienta por capacidades de detección ni la más barata, pero sí la que ofrece menor fricción si ya pagas Hub. Para equipos medianos sin security champions dedicados, esa fricción baja es lo que determina si la herramienta se usa o se deja de lado. Para equipos con cultura open source establecida o requisitos de auditabilidad, Trivy sigue siendo la elección correcta.