IEC 62443: OT Cybersecurity Explained for IT Teams
Actualizado: 2026-05-03
IEC 62443 is the international standard for cybersecurity in industrial control systems (ICS). It is critical for plants, utilities and infrastructure, and parallels ISO 27001 for IT but adapted to OT specifics: functional safety, real-time requirements and legacy equipment. With the NIS2 push, companies with OT environments must master it. This article offers a view oriented towards IT teams working alongside OT.
Key takeaways
- IEC 62443 segments industrial networks into zones connected by conduits with defined security controls.
- Defines four Security Levels (SL 1-4) based on the attacker sophistication the system must resist.
- Distinguishes three roles with distinct obligations: asset owner, system integrator, and product supplier.
- The seven Foundational Requirements (FR) are the basis of all compliance assessments.
- IT/OT coordination is key: IT teams contribute segmentation and monitoring, but must not apply IT practices without understanding the OT impact.
Why IT Teams Should Know It
IT/OT convergence is blurring lines that once separated both worlds. Specific reasons an IT team needs to understand IEC 62443:
- NIS2 requires many companies to integrate OT security into their overall cybersecurity programme.
- Effective coordination: IT cybersecurity must align with OT controls to avoid blind spots.
- Audit: IT teams increasingly audit OT environments under regulatory compliance requests.
- Incidents: Colonial Pipeline, Oldsmar and others show the risk is not theoretical.
IEC 62443 Structure
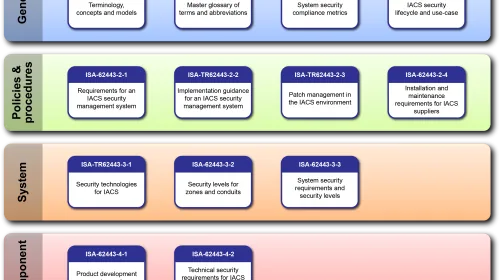
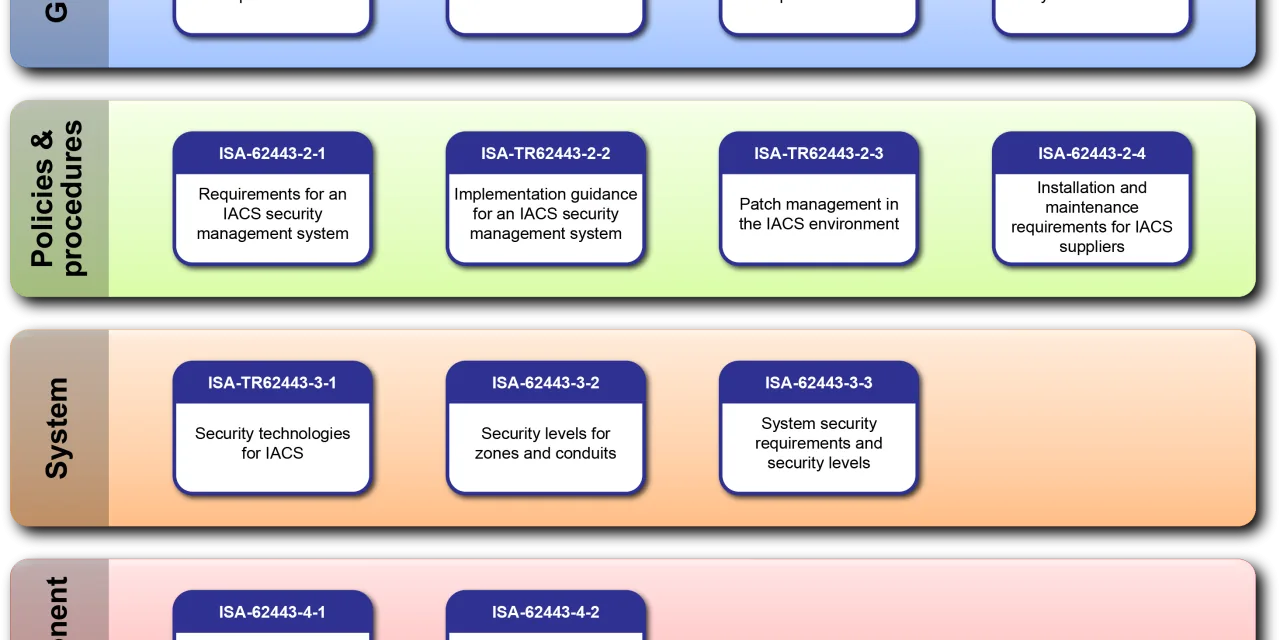
The standard organises into four series blocks:
- 62443-1-x: general (terminology, concepts, maturity models).
- 62443-2-x: policies and procedures (risk management, patching, third-party access).
- 62443-3-x: system requirements (architecture, risk assessment).
- 62443-4-x: component requirements (secure development lifecycle, product).
This structure allows incremental adoption: a team can start with system requirements (3-3) without waiting to master all blocks.
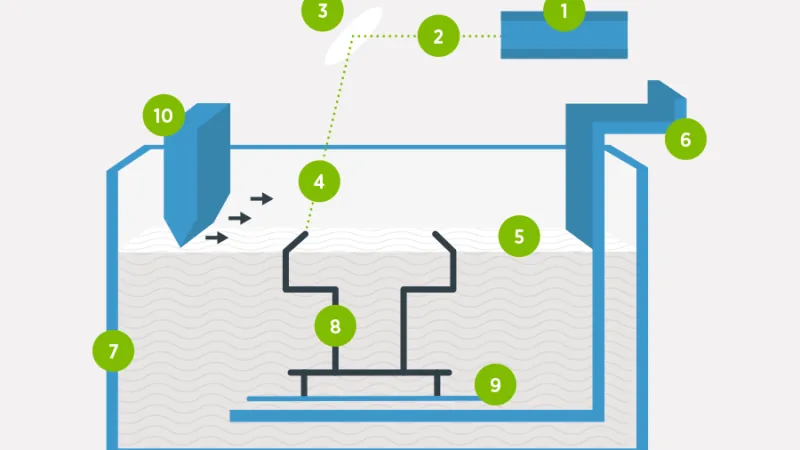
Zones and Conduits
The central concept is segmentation into zones connected by conduits:
- Zone: grouping of assets with similar security requirements.
- Conduit: communication path between zones with defined security controls.
- Trust boundaries: explicit and documented.
Similar to IT DMZ but formalised for industrial environments, where physical topology and availability requirements impose additional constraints.
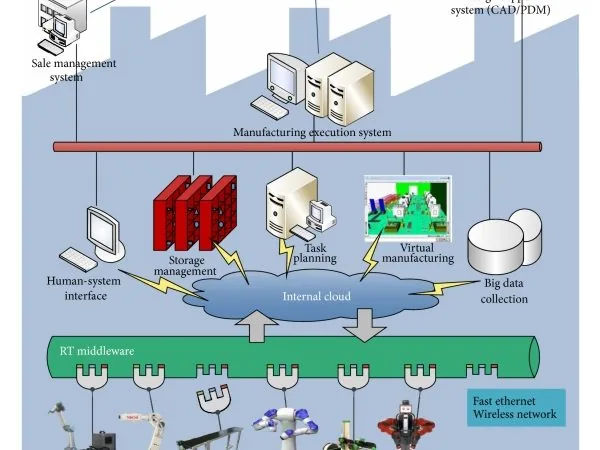
The Purdue Model
IEC 62443 conceptually incorporates the Purdue model as architectural reference:
- Level 0: sensors, actuators.
- Level 1: PLCs, RTUs.
- Level 2: SCADA, HMI.
- Level 3: manufacturing operations (MES).
- Level 3.5: industrial DMZ.
- Levels 4-5: enterprise IT.
Security Levels (SL)
62443 defines four target security levels:
- SL 1: protection against casual or inadvertent access.
- SL 2: resistance to intentional attacks with simple means.
- SL 3: resistance to intentional attacks with sophisticated means.
- SL 4: resistance to sophisticated attacks with extensive resources (nation-state attacker).
The Seven Foundational Requirements
The standard articulates seven Foundational Requirements (FR) that underlie all assessments:
- IAC — Identification and Authentication Control.
- UC — Use Control.
- SI — System Integrity.
- DC — Data Confidentiality.
- RDF — Restricted Data Flow.
- TRE — Timely Response to Events.
- RA — Resource Availability.
IEC 62443 vs ISO 27001
| Aspect | IEC 62443 | ISO 27001 |
|---|---|---|
| Focus | OT / industrial | IT / information security |
| Functional safety | Critical | Not primary |
| Legacy equipment | Accommodated | Less considered |
| Real-time | Considered | Not applicable |
| Certifications | Multiple routes | ISMS |
| Complementary | Yes | Yes |
Common IT Mistakes in OT
- Aggressive patching: OT patches require planned maintenance windows and functional safety validation.
- Hot updates: many OT systems do not support updates without downtime.
- Standard IT cryptography: OT may need lighter algorithms due to real-time constraints.
- “IT best practices” without adaptation: applied without context can break real-time or availability guarantees.
Conclusion
IEC 62443 is the reference framework for industrial cybersecurity, and understanding it has become mandatory for IT teams operating in companies with OT environments. IT/OT convergence and NIS2 regulatory pressure make this integration inevitable. The path is not “adopt everything at once” but a gradual process starting with inventory, continuing with zone segmentation, and consolidating with risk-prioritised controls. Industrial infrastructure attacks are not hypothetical: they are an operational risk requiring coordinated response across both domains.