IEC 62443: ciberseguridad OT explicada para equipos IT
Índice de contenidos
- Puntos clave
- Por qué los equipos IT deben conocerlo
- Estructura de IEC 62443
- Zonas y conductos
- El modelo Purdue
- Niveles de seguridad (SL)
- Los siete requisitos fundacionales
- Certificaciones disponibles
- IEC 62443 frente a ISO 27001
- Coordinación IT/OT: qué aporta IT
- Errores comunes de los equipos IT en OT
- Tecnologías relevantes para el entorno OT
- Fases de implementación típicas
- Conclusión
Actualizado: 2026-05-03
IEC 62443 es el estándar internacional para ciberseguridad en sistemas de control industrial (ICS). Es crítico para plantas, utilities e infraestructuras, y guarda paralelismos con ISO 27001 para IT pero adaptado a las especificidades de OT: seguridad funcional, tiempo real y equipos heredados. Con la presión de NIS2, las empresas con entornos OT necesitan conocerlo a fondo. Este artículo ofrece una visión orientada a equipos IT que trabajan junto a OT.
Puntos clave
- IEC 62443 segmenta la red industrial en zonas conectadas por conductos con seguridad definida.
- Define cuatro niveles de seguridad (SL 1-4) según la sofisticación del atacante que el sistema debe resistir.
- Distingue tres roles con obligaciones distintas: propietario del activo, integrador de sistemas y proveedor de componentes.
- Los siete requisitos fundacionales (FR) son la base de todas las evaluaciones de cumplimiento.
- La coordinación IT/OT es clave: los equipos IT contribuyen con segmentación y monitorización, pero no deben aplicar prácticas IT sin entender el impacto en OT.
Por qué los equipos IT deben conocerlo
La convergencia IT/OT borra las líneas que antes separaban ambos mundos. Las razones concretas por las que un equipo IT necesita entender IEC 62443 son:
- NIS2 obliga a muchas empresas a integrar la seguridad OT en su programa general de ciberseguridad.
- Coordinación efectiva: la ciberseguridad IT debe alinearse con los controles OT para evitar puntos ciegos.
- Auditoría: los equipos IT auditan cada vez más entornos OT bajo petición de cumplimiento regulatorio.
- Incidentes: Colonial Pipeline, Oldsmar y otros casos demuestran que el riesgo no es teórico.
Estructura de IEC 62443
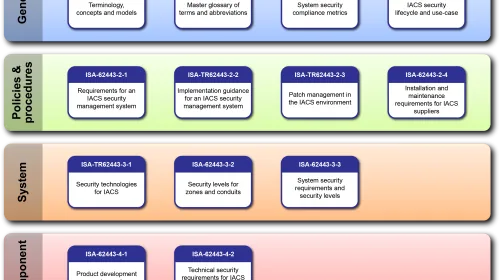
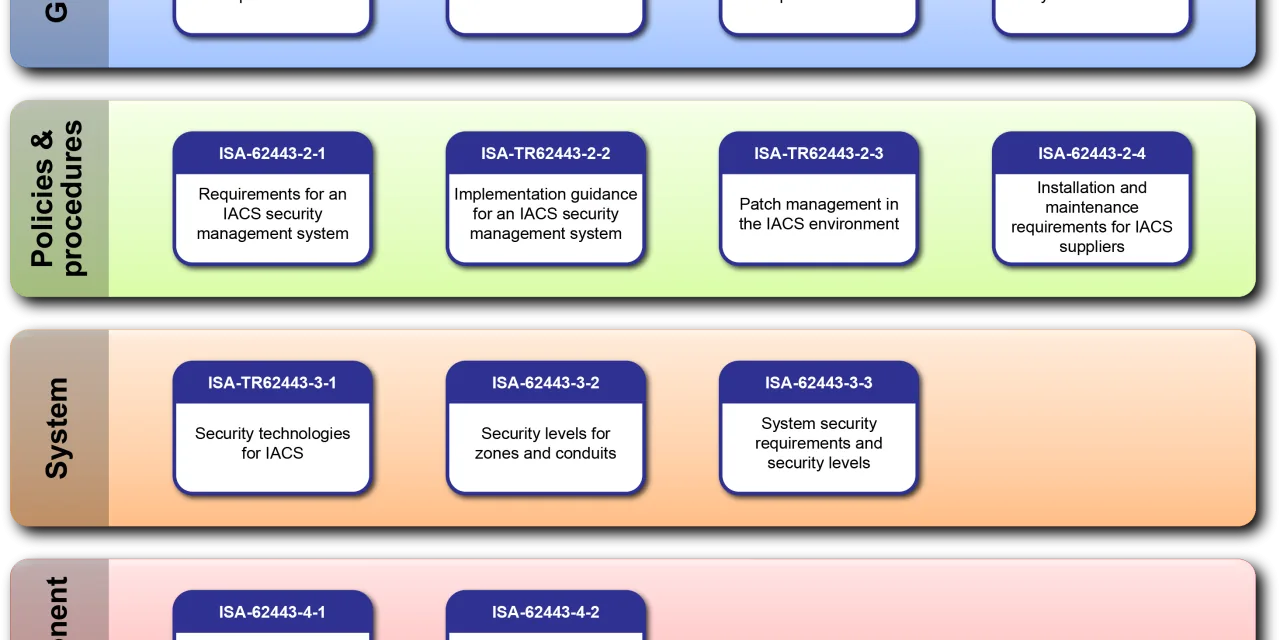
La norma se organiza en cuatro bloques de series:
- 62443-1-x: general (terminología, conceptos, modelos de madurez).
- 62443-2-x: políticas y procedimientos (gestión de riesgo, parches, acceso de terceros).
- 62443-3-x: requisitos de sistema (arquitectura, evaluación de riesgos).
- 62443-4-x: requisitos de componente (ciclo de desarrollo seguro, producto).
Esta estructura permite aplicar la norma de forma incremental: un equipo puede empezar por los requisitos de sistema (3-3) sin esperar a dominar todos los bloques.
Zonas y conductos
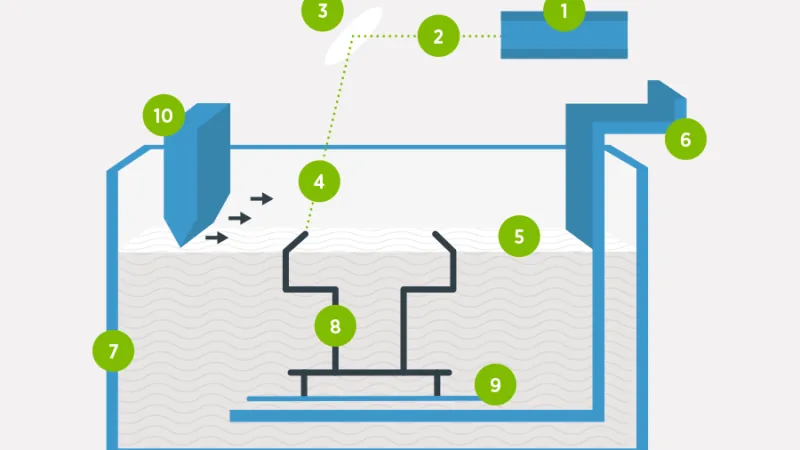
El concepto central es la segmentación en zonas conectadas por conductos:
- Zona: agrupación de activos con requisitos de seguridad similares.
- Conducto: ruta de comunicación entre zonas con controles de seguridad definidos.
- Fronteras de confianza: explícitas y documentadas.
Es similar a la DMZ IT pero formalizado para entornos industriales, donde la topología física y los requisitos de disponibilidad imponen restricciones adicionales.
El modelo Purdue
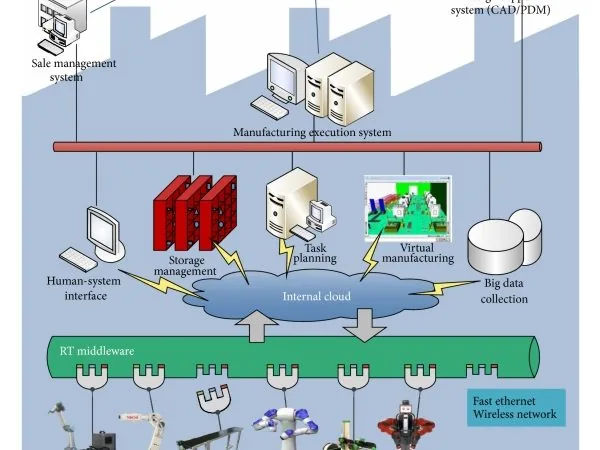
IEC 62443 incorpora conceptualmente el modelo Purdue como referencia arquitectónica:
- Nivel 0: sensores, actuadores.
- Nivel 1: PLCs, RTUs.
- Nivel 2: SCADA, HMI.
- Nivel 3: operaciones de fabricación (MES).
- Nivel 3.5: DMZ industrial.
- Niveles 4-5: IT empresarial.
Este modelo orienta la segmentación en zonas: cada nivel tiene requisitos de seguridad distintos y las comunicaciones entre niveles deben pasar por conductos controlados.
Niveles de seguridad (SL)
62443 define cuatro niveles de seguridad objetivo:
- SL 1: protección frente a acceso casual o involuntario.
- SL 2: resistencia a ataques intencionales con medios simples.
- SL 3: resistencia a ataques intencionales con medios sofisticados.
- SL 4: resistencia a ataques sofisticados con recursos extensos (atacante de estado-nación).
El ejercicio práctico consiste en evaluar el SL objetivo de cada zona en función del impacto de un incidente y aplicar los controles que corresponden a ese nivel.
Los siete requisitos fundacionales
La norma articula siete Foundational Requirements (FR) que son la base de todas las evaluaciones:
- IAC — Identification and Authentication Control.
- UC — Use Control.
- SI — System Integrity.
- DC — Data Confidentiality.
- RDF — Restricted Data Flow.
- TRE — Timely Response to Events.
- RA — Resource Availability.
Cada FR se desglosa en requisitos específicos por nivel de seguridad, lo que permite construir una hoja de ruta de implementación priorizada.
Certificaciones disponibles
El ecosistema de certificación es más maduro que hace tres años. Las rutas disponibles son:
- IEC 62443-2-4: para integradores de sistemas.
- IEC 62443-3-3: a nivel de sistema.
- IEC 62443-4-1: ciclo de desarrollo seguro para fabricantes.
- IEC 62443-4-2: a nivel de componente.
La demanda de certificación viene impulsada tanto por clientes industriales como por requisitos regulatorios en sectores de infraestructura crítica.
IEC 62443 frente a ISO 27001
| Aspecto | IEC 62443 | ISO 27001 |
|---|---|---|
| Foco | OT / industrial | IT / seguridad de la información |
| Seguridad funcional | Crítica | No es objetivo primario |
| Equipos heredados | Contemplados | Menos considerados |
| Tiempo real | Considerado | No aplicable |
| Certificaciones | Múltiples rutas | SGSI |
| Complementarios | Sí | Sí |
La recomendación es usar ambos: ISO 27001 para el entorno empresarial IT y 62443 para las zonas OT. NIS2 reconoce IEC 62443 como marco válido y su adopción facilita la demostración de cumplimiento regulatorio.
Coordinación IT/OT: qué aporta IT
Los equipos IT tienen capacidades valiosas para el entorno OT:
- Segmentación de red mediante VLANs y firewalls industriales.
- Monitorización: ingestión de logs OT en el SIEM corporativo.
- Respuesta a incidentes: alineación de procedimientos entre dominios.
- Gestión de identidad: federación entre dominios con protocolos adecuados.
- Gestión de parches: con cadencia diferente pero coordinada.
Lo que IT no debe hacer: cambiar configuraciones OT sin validar el impacto en seguridad funcional y disponibilidad. Los sistemas de control no son servidores web; un reinicio imprevisto puede tener consecuencias físicas.
Errores comunes de los equipos IT en OT
- Parchear agresivamente: los parches OT requieren ventanas de mantenimiento planificadas y validación de seguridad funcional.
- Aplicar actualizaciones en caliente: muchos sistemas OT no admiten actualizaciones sin parada.
- Criptografía IT estándar: los sistemas OT pueden necesitar algoritmos más ligeros por restricciones de tiempo real.
- “Las mejores prácticas IT” sin adaptación: aplicadas sin contexto pueden romper garantías de tiempo real o disponibilidad.
Respetar la experiencia de los equipos OT no es opcional. El conocimiento del proceso industrial es tan crítico como el conocimiento de ciberseguridad.
Tecnologías relevantes para el entorno OT
El stack tecnológico específico para este ámbito incluye:
- Firewalls industriales: Moxa, Hirschmann, Fortinet FortiGate Rugged.
- Diodos de datos: para comunicación unidireccional en zonas críticas.
- IDS industrial: Claroty, Nozomi, Dragos.
- Integración SIEM con OT: módulos OT de Splunk, QRadar.
- Gestión de parches OT: herramientas especializadas como Verve.
Fases de implementación típicas
El recorrido habitual de una organización que adopta IEC 62443 sigue estas etapas:
- Inventario de activos OT: a menudo inexistente o incompleto al inicio.
- Diagrama de zonas y conductos: mapa de la red industrial real.
- Evaluación de riesgos: por zona y conducto, con niveles SL objetivo.
- Análisis de brechas frente a 62443.
- Implementación priorizada de controles según impacto.
- Mejora continua con revisiones periódicas.
Es un proceso de años, no de meses. Lo importante es empezar con el inventario y el diagrama; sin ellos, cualquier otra actividad es ciega.
Conclusión
IEC 62443 es el marco de referencia para ciberseguridad industrial, y su conocimiento se ha vuelto obligatorio para equipos IT que operan en empresas con entornos OT. La convergencia IT/OT y la presión regulatoria de NIS2 hacen inevitable esta integración. El camino no es “adoptar todo de golpe”, sino un proceso gradual que empieza por el inventario, sigue con la segmentación en zonas, y se consolida con controles prioritzados por nivel de riesgo. Los ataques a infraestructura industrial no son hipotéticos: son un riesgo operativo que requiere respuesta coordinada entre ambos dominios.